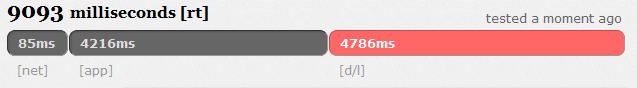
The exchange of information is greater today than ever before in our history. This means that the threat of evil misusing these standard channels of communication to send stolen information or a plan against a nation is more likely now than ever (Goel, Garuba, Liu, & Nguyen, 2007). After the attack of 9-11 it was believed that terrorist were hiding information in pictures using steganography. The goal of this research paper is to discuss ways in which steganography can be detected.
To understand methods of detecting steganography, it is necessary to define what steganography is and how it works. Steganography is a general term for a process of hiding information. The word Steganography has its origin in the Greek language, meaning “covered writing” (Johnson & Jajodia, 1998). Most commonly steganography will be used to hide messages.
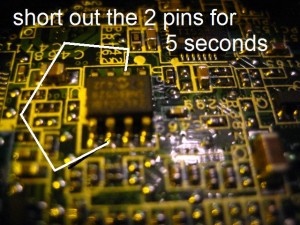
Steganographic data is mostly hidden within a picture file. The data or message can be stored as a picture hidden within a picture or in the lower level bits of a picture file. A few other common file types which can be utilized by steganography include audio and document files. These are more difficult to create then a picture file. They do offer increased protection against detection (Artz, 2001).
The data is either stored as a picture hidden within the main picture, or in the data that makes up the bits of the picture file. Other common file types utilized by steganography include document files and audio files, both of which are much harder to create then a steganographic picture file, but offer increased protection against detection (Artz, 2001).
Like many security applications and tools, steganography can be used for a variety of reasons. Some good purposes could include things like watermarking images for reasons such as copyright protection. Digital watermarks (also known as fingerprinting, are especially important in copyright material) are similar to steganography in that the watermark is overlaid and appear to be part of the original file and are thus not easily detectable by the average person. Another use would be to tag notes to online images.
Read entire paper @ google docs.